Biturai Trading Wiki
The ultimate crypto encyclopedia. Verified by experts.

PLONK: The Zero-Knowledge Proof Powerhouse
PLONK is a cutting-edge cryptographic protocol that enables **Zero-Knowledge Proofs (ZKPs)**. It allows for the verification of information without revealing the underlying data itself, revolutionizing fields like blockchain and data privacy.
Groth16: The Gold Standard of Zero-Knowledge Proofs
Groth16 is a powerful cryptographic system allowing the verification of statements without revealing the underlying data. It's a cornerstone technology in privacy-focused applications, enabling secure and efficient proof generation and verification.

ZK-STARKs Explained: Zero-Knowledge Proofs for a Secure Future
ZK-STARKs are a type of cryptographic proof system that allows you to prove something is true without revealing the underlying information. This technology is crucial for enhancing privacy and scalability in blockchain and other applications.
ZK-SNARKs Explained: The Crypto Privacy Powerhouse
ZK-SNARKs are a powerful cryptographic tool that allows for proving knowledge of information without revealing that information. This technology is revolutionizing data privacy and verification in the blockchain space.
BLS Signatures: The Revolutionary Crypto Signature Scheme
BLS signatures are a powerful cryptographic tool that simplifies and secures blockchain networks. They enable efficient signature verification and aggregation, improving scalability and reducing transaction costs.

Bloom Filter
A Bloom filter is a space-efficient data structure that tests whether an element is a member of a set. It works by probabilistically representing a set of data, allowing for quick membership checks while potentially yielding false positives.

Merkle Proofs Explained: Secure Blockchain Data Verification
Merkle proofs are a fundamental cryptographic tool for verifying data integrity in blockchains. They allow you to confirm that a specific piece of information is included in a larger dataset without needing to download the entire dataset.

DAOstack: The Operating System for Decentralized Governance
DAOstack is a platform designed to facilitate the creation and management of Decentralized Autonomous Organizations (DAOs). It provides the tools and infrastructure for groups to self-organize, make decisions, and manage resources in a transparent and efficient manner.

Bribe Protocol Deep Dive
Bribe protocols are a fascinating mechanism in decentralized finance, used to incentivize specific actions within a protocol, primarily to boost liquidity. These protocols involve payments to voters to influence decisions, creating a market for governance power and impacting the dynamics of DeFi platforms.
System Quality Number (SQN): A Deep Dive for Crypto Traders
The System Quality Number (SQN) is a powerful metric that assesses the quality and consistency of a trading system. It helps traders evaluate the profitability, risk, and overall robustness of their strategies, providing a more comprehensive view than simple expectancy.

Secp256k1: The Elliptic Curve Powering Bitcoin's Security
Secp256k1 is a mathematical curve that underpins the security of Bitcoin and many other cryptocurrencies. It’s the backbone for generating public and private keys, ensuring that transactions are secure and verifiable.
Blake2: The High-Performance Cryptographic Hash Function
Blake2 is a cryptographic hash function, designed for speed and security. It's used to generate a unique 'fingerprint' of data, ensuring data integrity and security in various applications.

RIPEMD-160: The Bitcoin Hash Function Explained
RIPEMD-160 is a cryptographic hash function used in Bitcoin to create shorter representations of data. It takes an input of any size and produces a fixed-size 160-bit output, often called a message digest, which is essential for Bitcoin address generation.

Radix Tree: A Deep Dive for Crypto Traders
A Radix Tree is a highly efficient data structure used to store and retrieve data, especially useful in blockchain technology. Understanding how Radix Trees work can provide insights into the inner workings of blockchains and improve your comprehension of crypto trading strategies.

Merkle Patricia Trie: The Blockchain Data Guardian
The Merkle Patricia Trie (MPT) is a sophisticated data structure at the heart of Ethereum, ensuring data integrity and efficient storage. It combines the strengths of Merkle Trees and Patricia Tries to create a robust system for managing blockchain data.

Storage Tree Explained: The Foundation of Blockchain Data
A Storage Tree, most commonly a **Merkle Tree**, is a fundamental data structure in blockchain technology. It efficiently organizes and verifies data, ensuring the integrity and security of transactions and other information stored on a blockchain.
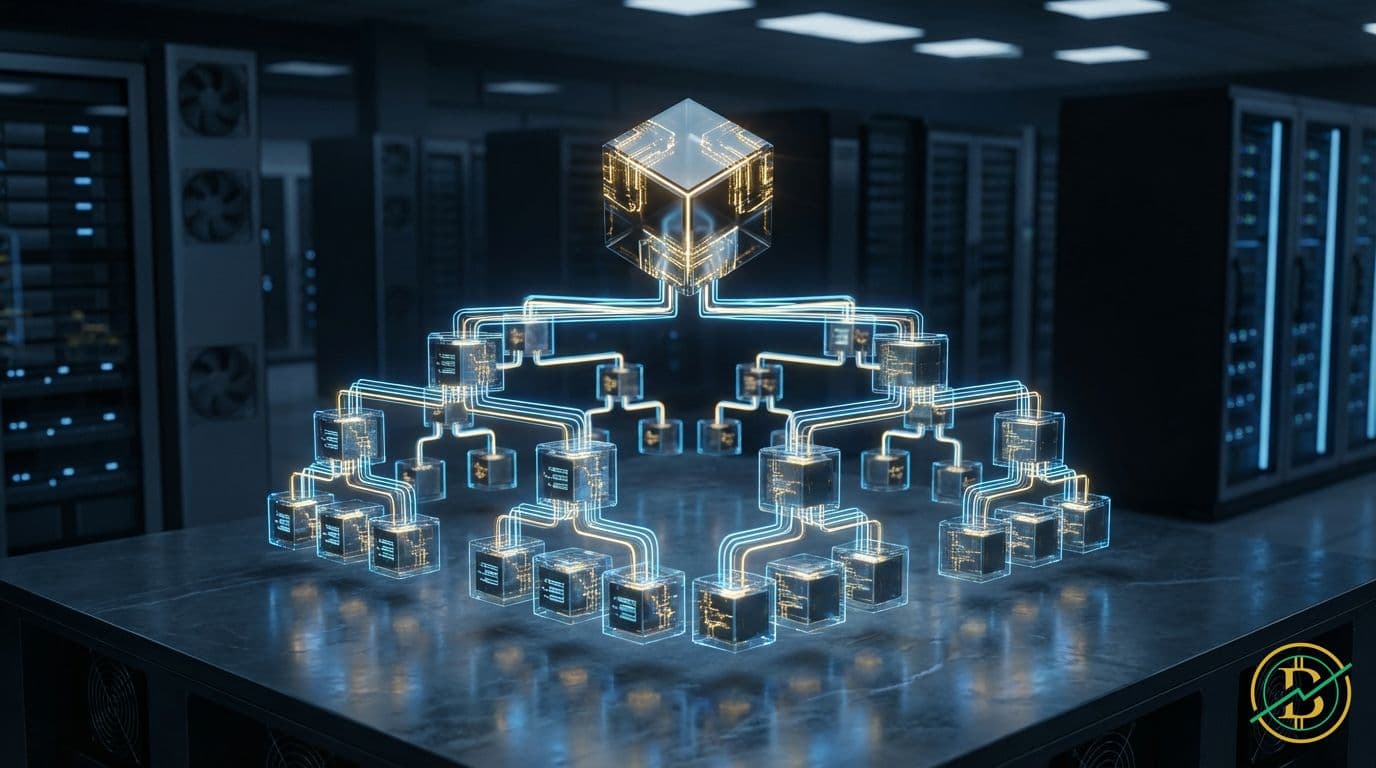
Merkle Root: The Blockchain's Transaction Fingerprint
A Merkle root is a fundamental concept in blockchain technology, representing a single hash that verifies all transactions within a block. It ensures data integrity and enables efficient transaction verification.

OpenZeppelin Governor: Decentralized Governance Explained
OpenZeppelin Governor is a smart contract module that enables on-chain governance for decentralized autonomous organizations (DAOs). It allows token holders to propose, vote on, and execute changes to a protocol or project, ensuring community control.

Governor Contract: Decentralized Governance in Crypto
Governor contracts are the cornerstone of decentralized autonomous organizations (DAOs), allowing token holders to collectively make decisions about a project. These contracts enable on-chain voting, proposal management, and execution of actions, fostering community control and transparency.
Timelock Controller: Protecting Your Crypto with Time
A Timelock Controller is a crucial smart contract component that introduces time delays to transactions, enhancing security and governance. This prevents immediate execution of critical actions, providing a buffer against malicious attacks and enabling a more considered decision-making process.